
Key-Value Stores Aren't Simple
The 3-method API hides 5 design dimensions — durability, consistency, latency, sharding, hot keys — and ZippyDB, Panda, and Discord chose differently on every axis.
VISUAL SYSTEMS
Visual mental models for the systems you use but don't fully understand. No prerequisites. No hand-waving. Just clear, animated explanations.


The 3-method API hides 5 design dimensions — durability, consistency, latency, sharding, hot keys — and ZippyDB, Panda, and Discord chose differently on every axis.

Monolith or microservices? You've heard the debate a hundred times. The real question isn't architecture — it's whether one team's release is blocking another team's work. In 8 minutes: the strongest arguments on both sides, then the three questions that actually tell you which one's right for your team. → What microservices actually are (it's not about size — it's about independent deployability) → The case FOR, steelmanned: the Amazon API Mandate, and how Conway's Law bakes your org chart into your architecture → The case AGAINST, steelmanned: the tail-at-scale math that nukes fanout architectures, and the "distributed monolith" failure mode that eats most migrations → The three-question decision ladder that settles any architecture debate at your company → Why some of the most trafficked sites in the world still run monoliths — and why that's not an accident By the end, you'll stop having this argument in the abstract.
NumPy isn't really Python. It's a thin Python layer over a C core. A Python for-loop summing 100 million numbers takes 92 seconds. `np.arange(100_000_000).sum()` finishes in a third of a second — 300× faster, using the same Python you just wrote. Where did the speed come from? Python didn't suddenly get fast. The loop moved into C. → Why a Python list is a pointer chase and an ndarray is a wall of bytes → What a ufunc actually is, and why `arr + arr` becomes ONE C function call, not a million → How NumPy ships hand-tuned SIMD kernels (SSE, AVX, NEON) for every modern CPU → The stride trick: why `arr[::2]` doesn't copy — and why broadcasting is literally `stride = 0` → The "Python mask over C" pattern that powers pandas, PyTorch, scikit-learn By the end, that one-line `.sum()` is the least mysterious thing in your data science stack. Previous video (recommended first): "Why Python Is 100x Slower Than C" Chapters: 0:00 Intro 0:02 The puzzle — one line, 80× faster 0:38 Bytes, not objects — the memory layout trick 1:33 Ufuncs — one call, one C loop 2:37 Strides — slicing without copying 3:30 The Python mask over C 4:19 Outro References: → Harris et al. "Array programming with NumPy" (Nature 2020) — https://www.nature.com/articles/s41586-020-2649-2 → Jake VanderPlas "Losing Your Loops" (PyCon 2015) — https://youtu.be/EEUXKG97YRw → NumPy official internals docs — https://numpy.org/doc/stable/reference/internals.html #Python #NumPy #DataScience
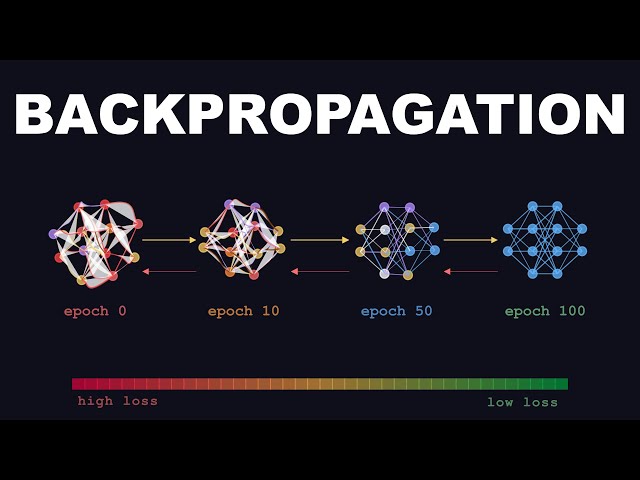
The chain rule meets gradient descent. Watch how neural networks learn by propagating errors backward through every layer.
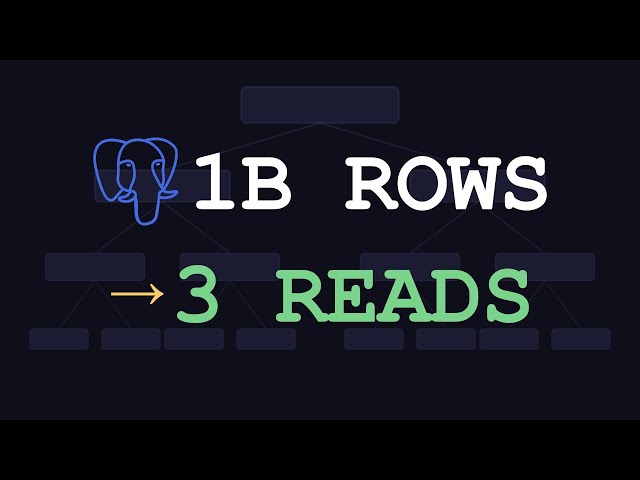
Every database you use is built on B-trees. See how they minimize disk I/O to search billions of rows efficiently.

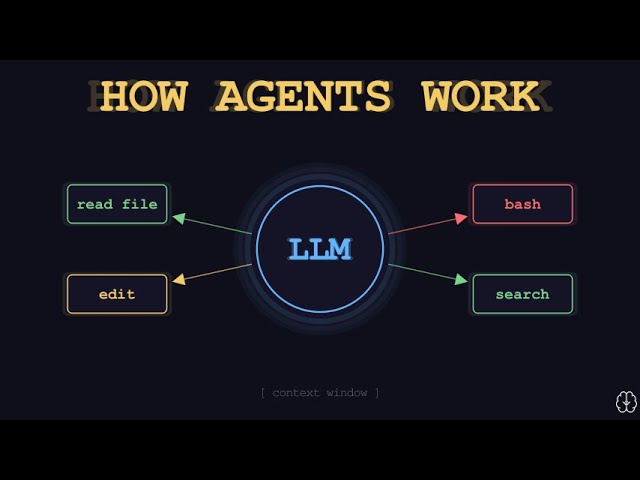
How do tools like Claude Code, Cursor, and Devin actually write code? The ReAct loop, tool calling, and context management — animated.
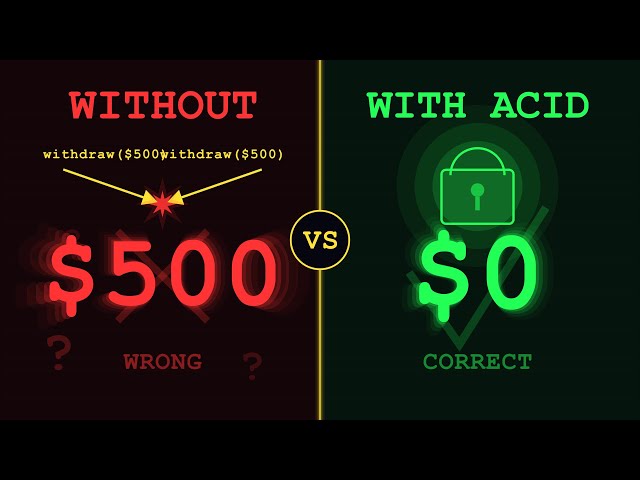
Two transfers hit at the same millisecond — your bank just created money out of thin air. ACID transactions prevent this.
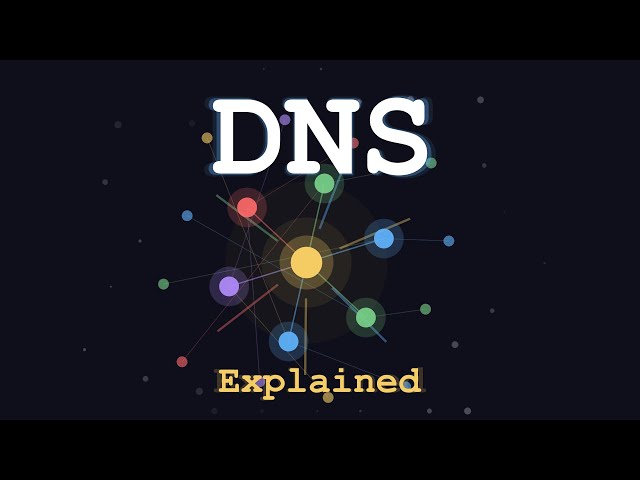
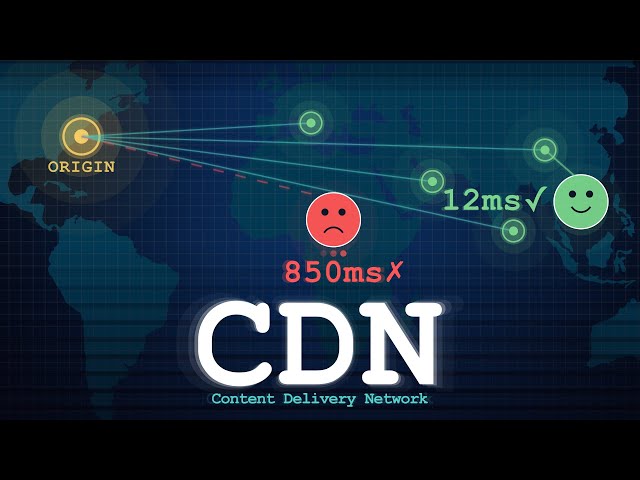
Every step of a DNS query visualized — from your browser's cache to root servers and back, in under 7 minutes.
Docker containers are not virtual machines. See how namespaces, cgroups, and union filesystems create isolated Linux processes.
The 5 generations of engineering that turned hot partitions into a solved problem — from consistent hashing to global admission control.
Words as vectors, sentences as geometry. How embedding spaces capture meaning and power modern AI — from Word2Vec to CLIP.
How JavaScript runs 1000 async tasks on a single thread. The call stack, task queue, microtask queue, and Web APIs — visualized.
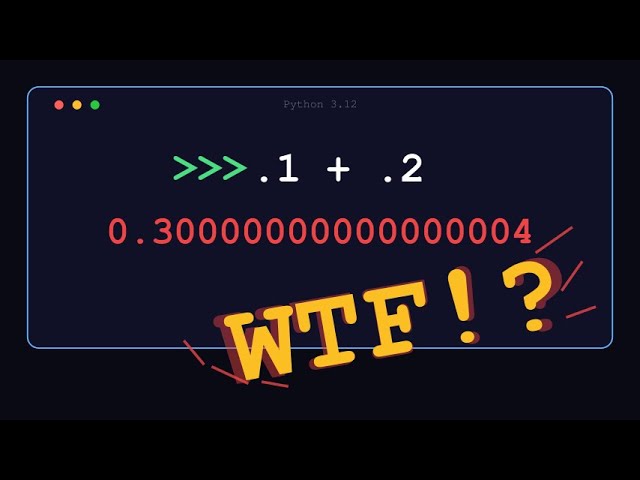
Why computers can't represent 0.1 exactly, and what IEEE 754 does about it. The sign-exponent-mantissa encoding, visualized.
Git is a content-addressable object store, not a diff tracker. See how blobs, trees, and commits actually work under the hood.

Most developers think git merge just combines two branches. The real algorithm finds a third file — the merge base — and does a three-way diff that resolves 95% of changes automatically.
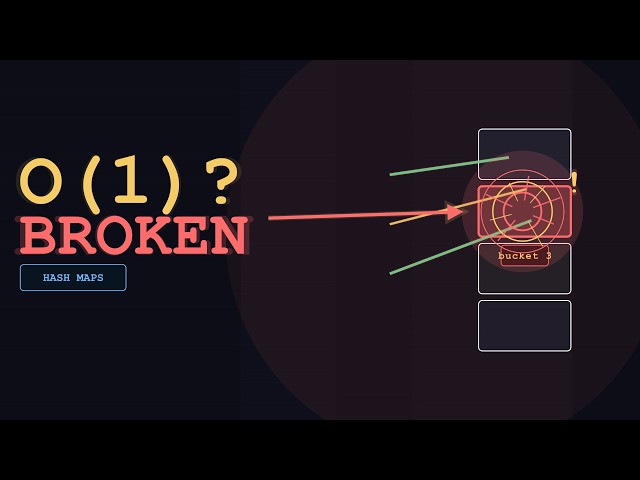
A deep dive into hash maps — from the core hash-to-index trick, through collisions and resizing, to how Python, Java, and Go implement them differently.
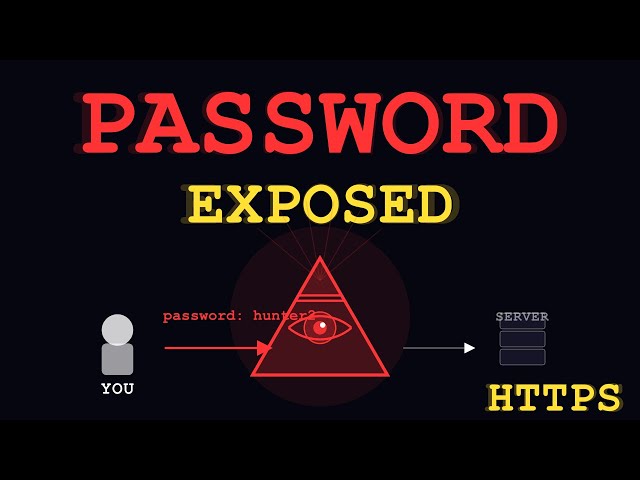
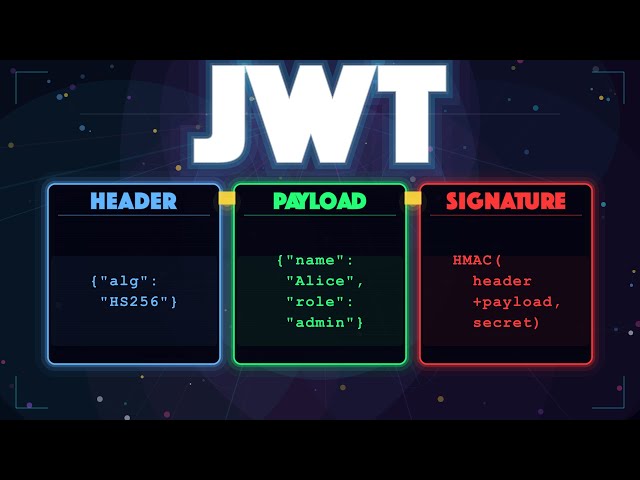
Most developers carry JWTs on every request but never look inside. The payload is plain text, the signature is the real security, and the alg:none attack broke everything.

Same data. JSON needs 41 bytes. Protobuf needs 12. But compactness isn't why Google built it. Watch the wire format, the varint bit-shift, and schema evolution — the three things JSON can't do.
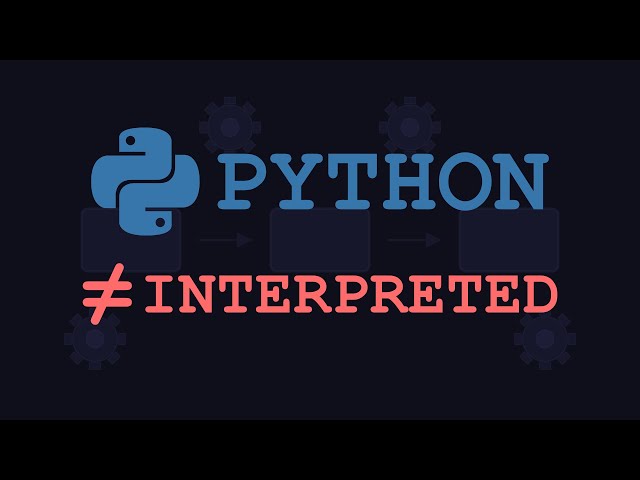
Python compiles to bytecode before interpreting it. See the hidden compiler, the dis module, and what actually runs when you hit Enter.
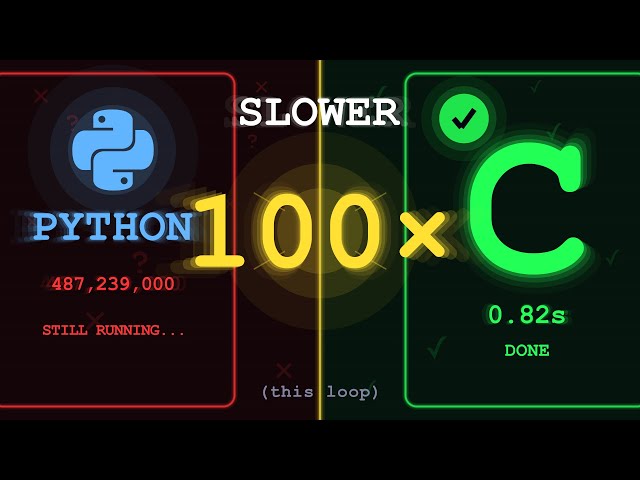
Same loop, same algorithm. C finishes in under a second. Python takes over a minute. The 100x isn't the GIL — it's what happens on every single iteration.
Recursion visualized from the ground up. Watch the call stack build, see Fibonacci branch into a tree, and understand why memoization changes everything.

Your regex compiles into a state machine every time it runs. NFA construction, DFA conversion, backtracking simulation, and the catastrophic ReDoS attack — all animated.


BPE, token boundaries, and glitch tokens — why language models see text differently than you do.
Self-attention, query-key-value, feed-forward networks, and generation — the full transformer architecture, animated step by step.
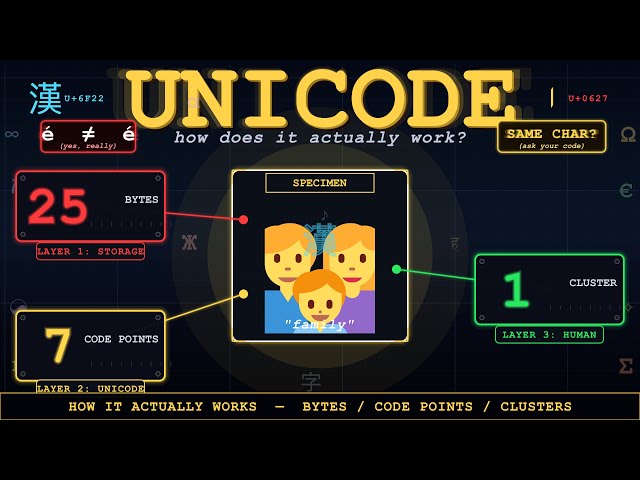
One emoji can be 25 bytes, 7 code points, and 1 grapheme cluster at the same time. This video explains the three layers underneath every string — ASCII's limit, Unicode code points, UTF-8 bytes, normalization, and why emoji make text handling such a trap.
Vim commands aren't random shortcuts — they're a composable language. Learn the verb + noun grammar, text objects, the dot command, and how the multiplication effect gives you hundreds of commands from a handful of building blocks.
Your program's memory addresses are a lie. Page tables, TLBs, and swap space — the OS abstraction that makes multitasking possible.

Every other video walks HTTP status codes numerically. This one walks them in the order your request actually meets them — connection, success, redirects, client errors, server errors. Fifteen codes, eight reveals, one mental map you'll keep. → The polite handshake before a big upload (100 Continue) → The redirect that broke every form on the web for 20 years (301), and the code created to fix it (308) → The cache check that returns no body — the smallest useful response on Earth (304) → Why 401 is misnamed and 404 is allowed to lie about what exists → The joke RFC the IETF tried to delete and the 15-year-old who saved it (418) → The Fahrenheit 451 reference hiding in HTTP (Tim Bray's transparency code) → Four 5xx codes, four different fingers pointing at four different broken links in the proxy chain (500, 502, 503, 504) By the end you'll stop memorizing codes and start reading them — every status code answers one question: where on the journey did this happen?
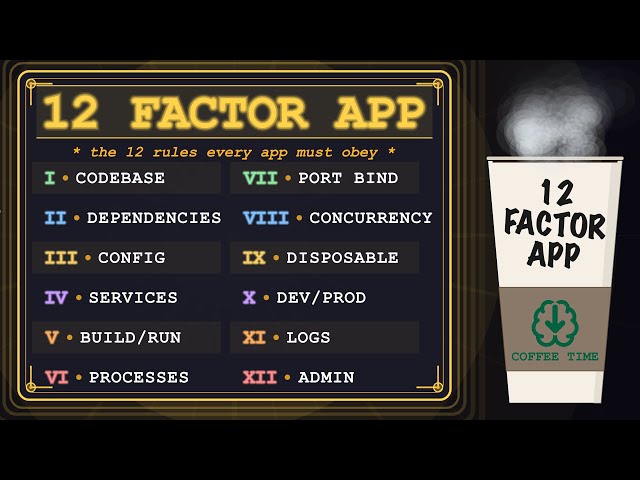
Twelve specific failure modes every production backend hits when it skips the 12 factor rules. Each factor: the concrete disaster if you skip it, then the fix.

Every 429 is the same HTTP code. Behind it, four completely different machines — fixed window, sliding window, token bucket, leaky bucket. Each one is a different answer to the same question: when does the server forget?
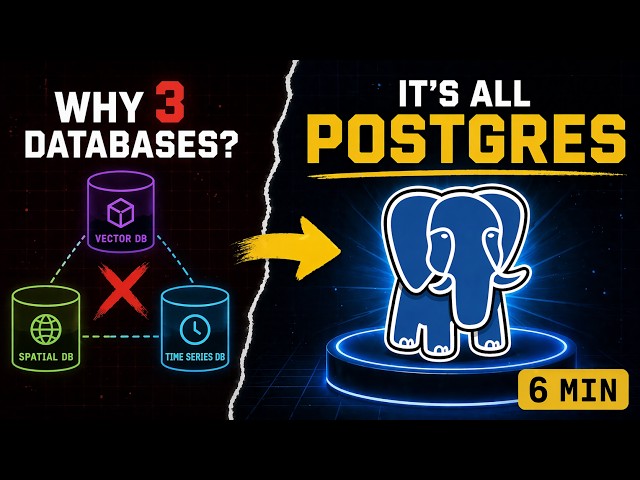
Postgres is the database that became a platform. In 6 minutes: why readers never wait for writers (MVCC), how EXPLAIN ANALYZE makes slow queries solvable, and the extension slot that turns the same engine into a vector DB, geospatial engine, and time-series store — all at once.
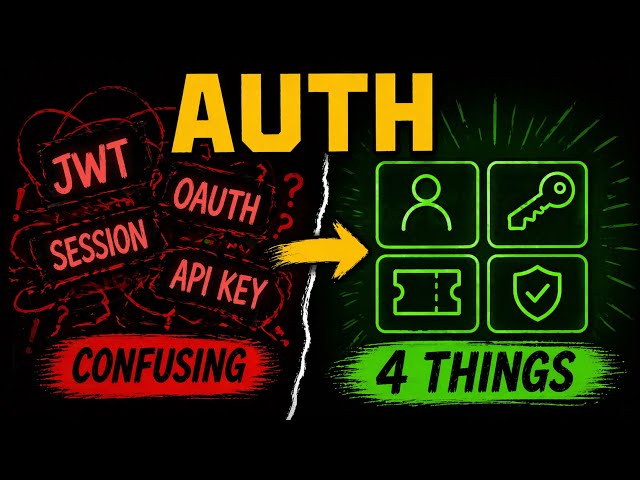
Every auth system — OAuth, JWT, session cookies, API keys, OIDC — is just four primitives composed differently: Identity, Credential, Session, Permission. Learn the model once; every auth doc you read afterward becomes trivial.
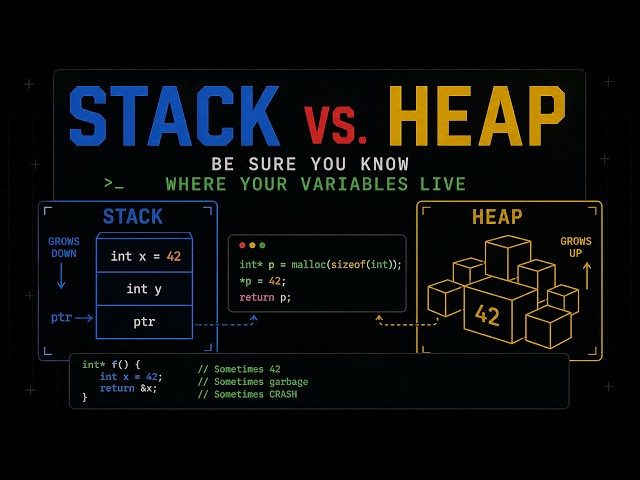
Stack allocation is one CPU instruction. Heap allocation is a bookkeeping operation. The choice isn't about size or speed — it's about lifetime. If your data must outlive the function that creates it, it cannot live on the stack. Period. Watch what allocation literally is on each side, and the dangling-pointer crash that's been silently waiting for you stops being mysterious.